10 000+ resultater for y12 computing

Unit 2 LO1 1.6 Information Formats
Ballong pop

Key words Unit 2
Wordsearch

TAKE 2: 2.1 Information Styles
Finn treffet

Take 2 Unit 2 5.2 DFDs
Bildequiz

Unit 1 LO5 Physical v Digital Security
Gruppe sortering

Internal & External Stakeholders
Gruppe sortering

Python Keywords Match-Up
Match opp

Organisational Security
Labyrintjakt

Communication skills in an IT environment
Wordsearch

Computer Hardware
Match opp

Unit 11 Revision
Match opp

LO4 4.3 Personal attributes
Wordsearch
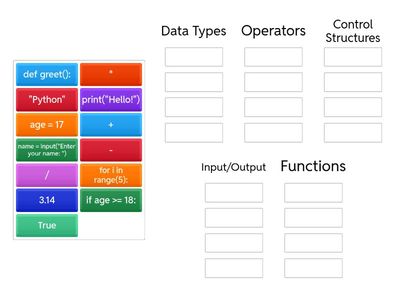
Group the Python Examples
Gruppe sortering

Take 2 3.6 Open v Closed Systems
Gruppe sortering

Take 3 3.5 Data Analysis Tools
Match opp

Key aspects of digital forensics
Match opp
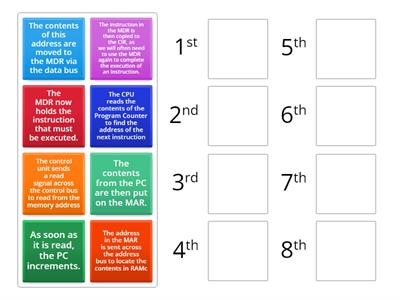
A-level FDE cycle: Order the steps for the FETCH process
Rangeringsrekkefølge
![3.5 Data Analysis Tools [2]](https://screens.cdn.wordwall.net/400/18a0e0cda7a1474daf031fdf03ad031d_22)
3.5 Data Analysis Tools [2]
Match opp

Take 2 6.1 Principles of Information Security
Gruppe sortering
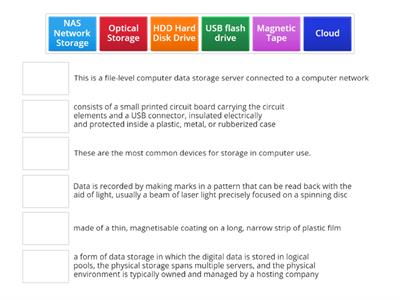
Types of Information Storage media
Match opp

What Is It?
Match opp
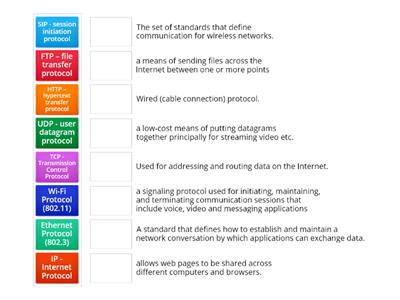
Protocols
Match opp

1.6 Information formats
Match opp

3.5 Data analysis tools
Bøddel

Unit 2 4.1 UK Legislation
Labyrintjakt

Unit 2 4.3 Green IT
Fullfør setningen

Take 2: Can you remember? LO2 2.4 Information Management
Merket diagram

TAKE 2 Unit 2 LO1 1.6 Information Formats
Ballong pop

Take 2 Unit 2 LO4 4.1 UK Legislation
Sann eller usann

Take 2 3.4 Stages of Data Analysis
Merket diagram

Take 3 Unit 2 1.2 Magnetic storage devices
Fullfør setningen

DPA - Personal or Senstive Data
Gruppe sortering

Internal threats
Spørrelek

BTEC: Implementation methods
Gruppe sortering

Headed Paper and Templates
Anagram

1.6 Information Formats
Whack-a-mole

LO4 Legislation protecting information
Se og husk
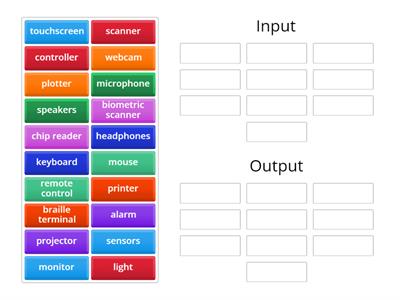
Input v Output
Gruppe sortering

BTEC Exam Keywords Crossword
Kryssord

Photoshop Tools
Anagram

1.4 Internet connections
Finn treffet

LO2 Key terms
Labyrintjakt
![2.2 Information Classification [Government documents]](https://screens.cdn.wordwall.net/400/302b93c7c6cf44afa2fa2506bef08cdd_48)
2.2 Information Classification [Government documents]
Gruppe sortering

Unit 2 Global Information 2.2 Information Classification
Quiz for spillshow





![Take 2 LO4: 4.1 UK Legislation [Match the Act]](https://screens.cdn.wordwall.net/400/fe615a2440a54d61aed9e3ebfa44e4ff_0)


![Take 2: 5.1 Data types and sources [2]](https://screens.cdn.wordwall.net/400/5f2cb3aaa7e94780a60abf16b2466aba_0)


![1.4 Internet [Connections Characteristics]](https://screens.cdn.wordwall.net/400/90473d4d853045d2a34089c9679f0da4_41)




