10 000+ výsledkov pre ' y12 computing '

Unit 2 LO1 1.6 Information Formats
Prepichni balóny

Key words Unit 2
Hľadanie slov

Unit 2 LO1 1.6 Information Formats - Second time lucky
Prepichni balóny

TAKE 2: 2.1 Information Styles
Nájdi zodpovedajúcu položku

Take 2 Unit 2 5.2 DFDs
Kvíz s obrázkami

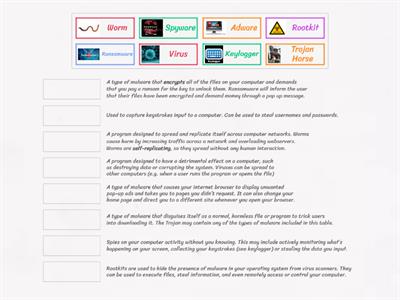
Unit 1 LO5 Physical v Digital Security
Zoradenie skupiny

Internal & External Stakeholders
Zoradenie skupiny

Python Keywords Match-Up
Spájačka

Organisational Security
Labyrint

Communication skills in an IT environment
Hľadanie slov

Computer Hardware
Spájačka

Unit 11 Revision
Spájačka

LO4 4.3 Personal attributes
Hľadanie slov
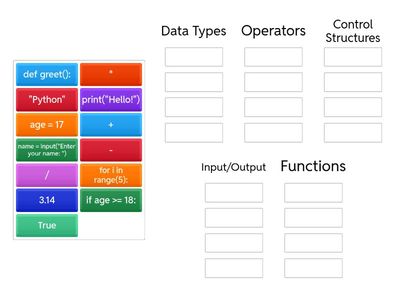
Group the Python Examples
Zoradenie skupiny

Take 2 3.6 Open v Closed Systems
Zoradenie skupiny

Take 3 3.5 Data Analysis Tools
Spájačka

Key aspects of digital forensics
Spájačka
![3.5 Data Analysis Tools [2]](https://screens.cdn.wordwall.net/400/18a0e0cda7a1474daf031fdf03ad031d_22)
3.5 Data Analysis Tools [2]
Spájačka

Take 2 6.1 Principles of Information Security
Zoradenie skupiny
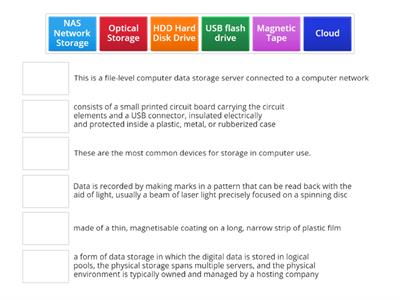
Types of Information Storage media
Spájačka

What Is It?
Spájačka
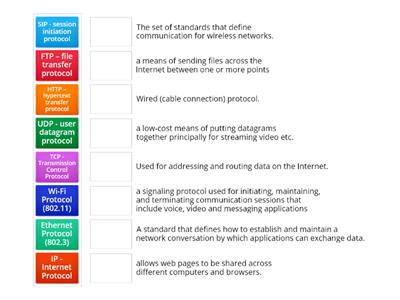
Protocols
Spájačka

1.6 Information formats
Spájačka

3.5 Data analysis tools
Šibenica

Unit 2 4.1 UK Legislation
Labyrint

Unit 2 4.3 Green IT
Doplňte vetu

Take 2: Can you remember? LO2 2.4 Information Management
Označený diagram

TAKE 2 Unit 2 LO1 1.6 Information Formats
Prepichni balóny

Take 2 Unit 2 LO4 4.1 UK Legislation
Pravda alebo nepravda

Take 2 3.4 Stages of Data Analysis
Označený diagram

Take 3 Unit 2 1.2 Magnetic storage devices
Doplňte vetu

DPA - Personal or Senstive Data
Zoradenie skupiny

Internal threats
Kvíz

BTEC: Implementation methods
Zoradenie skupiny

Headed Paper and Templates
Anagram

1.6 Information Formats
Omráč krtka

LO4 Legislation protecting information
Sledujte a zapamätajte si
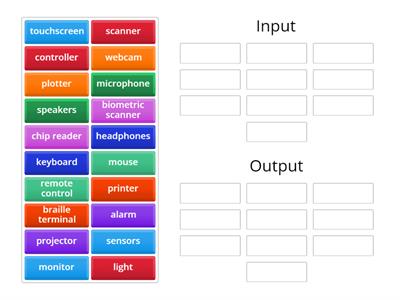
Input v Output
Zoradenie skupiny

BTEC Exam Keywords Crossword
Krížovka

Photoshop Tools
Anagram

1.4 Internet connections
Nájdi zodpovedajúcu položku

LO2 Key terms
Labyrint
![2.2 Information Classification [Government documents]](https://screens.cdn.wordwall.net/400/302b93c7c6cf44afa2fa2506bef08cdd_48)
2.2 Information Classification [Government documents]
Zoradenie skupiny

Unit 2 Global Information 2.2 Information Classification
Televízny kvíz




![Take 2 LO4: 4.1 UK Legislation [Match the Act]](https://screens.cdn.wordwall.net/400/fe615a2440a54d61aed9e3ebfa44e4ff_0)


![Take 2: 5.1 Data types and sources [2]](https://screens.cdn.wordwall.net/400/5f2cb3aaa7e94780a60abf16b2466aba_0)


![1.4 Internet [Connections Characteristics]](https://screens.cdn.wordwall.net/400/90473d4d853045d2a34089c9679f0da4_41)




