Cybersecurity
Wymagana subskrypcja
Liczba wyników dla zapytania „cybersecurity”: 911

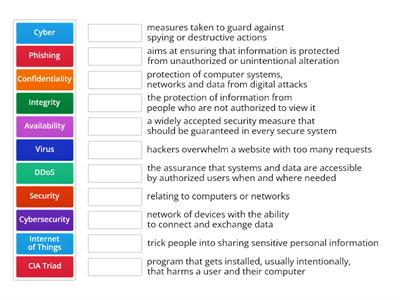
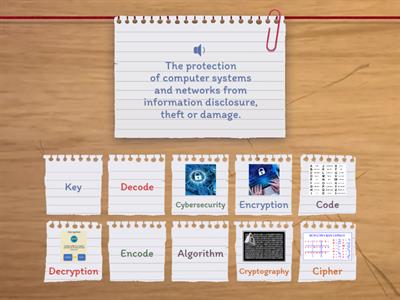
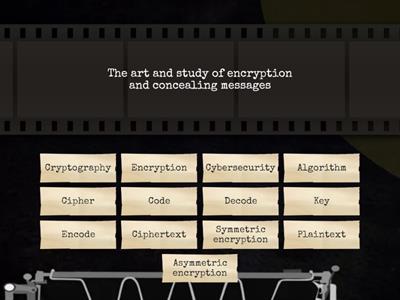
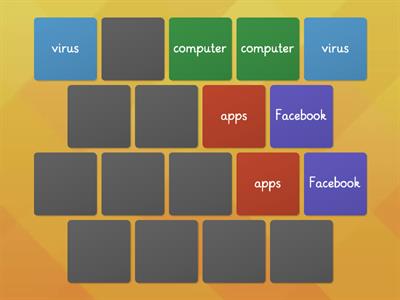
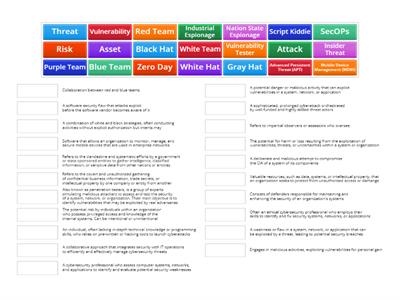
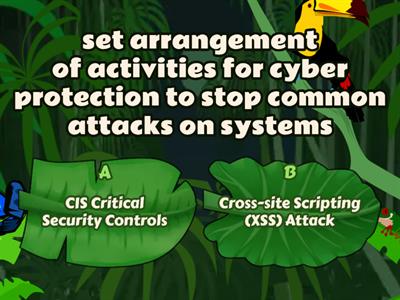
Cybersecurity Collocations
Znajdź parę

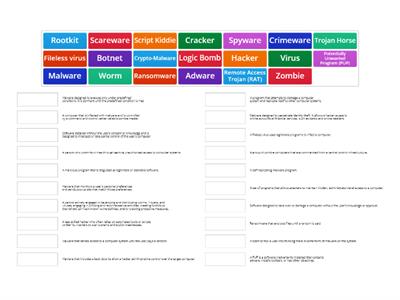
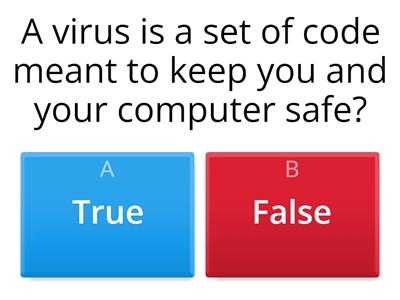
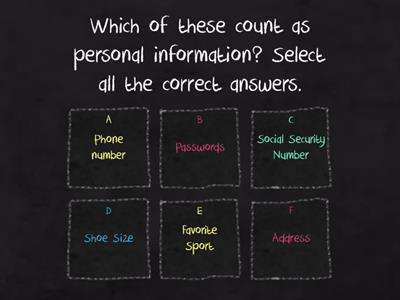
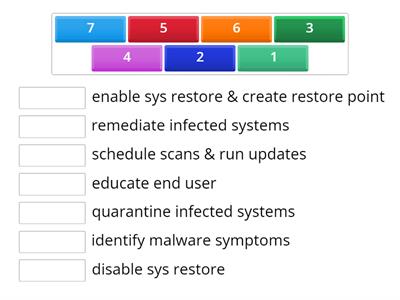
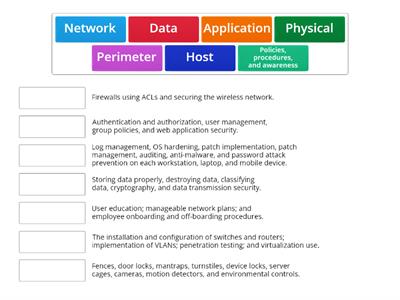
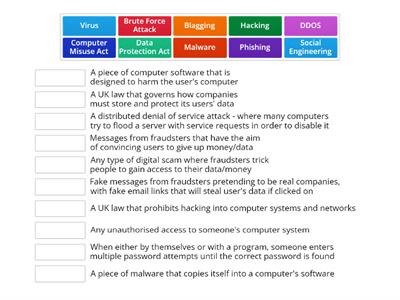
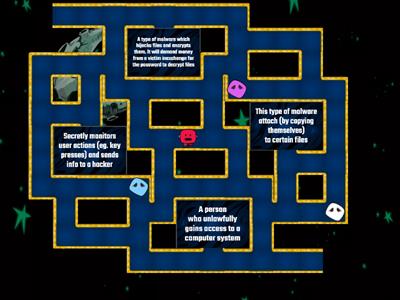
Cybersecurity threats
Połącz w pary

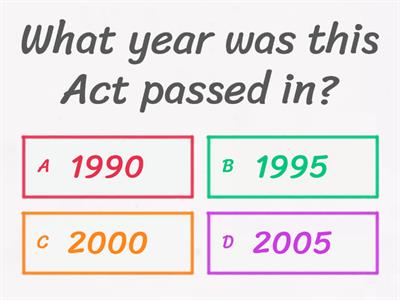
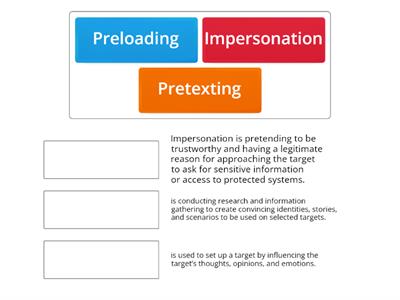
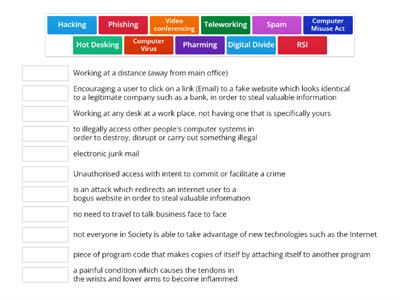
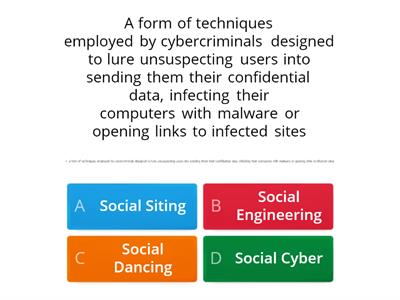
Phishing and scams
Test

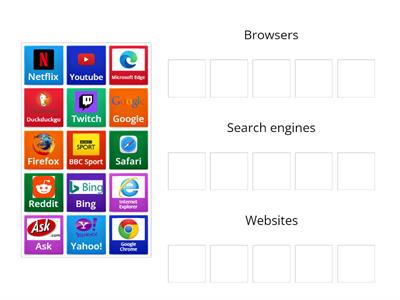
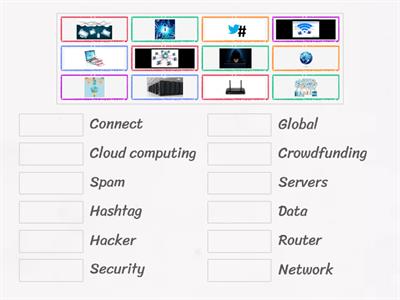
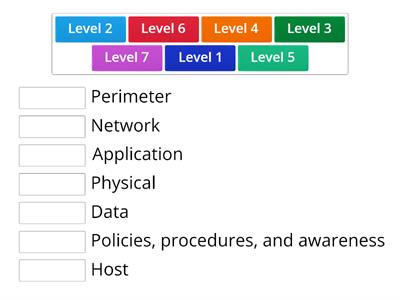
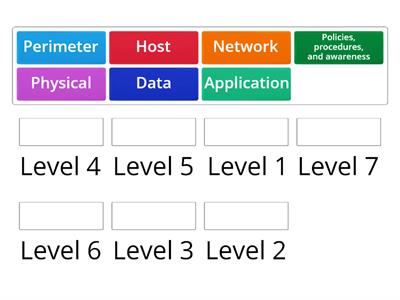
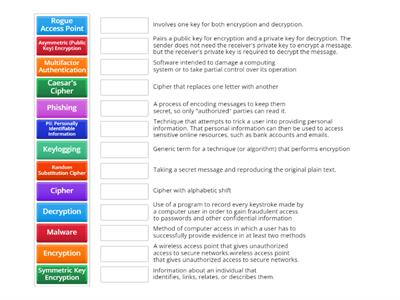
Computer Technology Introduction
Połącz w pary